The seamless integration of kinetic military operations with retaliatory digital strikes has transformed the domestic landscape into an active theater of war where every connected device serves as a potential entry point for foreign adversaries. As military engagements in the Middle East intensify, the repercussions are no longer confined to distant borders but manifest in the silent infiltration of American power grids and municipal water systems. This convergence of traditional warfare and cyber aggression necessitates a fundamental reassessment of what constitutes national defense in the current era. The present geopolitical landscape reveals that while the military maintains air and sea superiority, the digital front remains porous and unpredictable.
The Digital Battlefield: Assessing the State of National Cyber Resilience
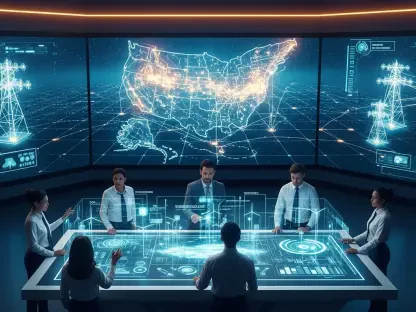
Modern conflict dictates that domestic infrastructure is the primary target for asymmetric retaliation, turning utility companies and local governments into frontline participants in global disputes. The intersection of kinetic warfare and digital retaliation has created a complex environment where the lines between civilian and military targets are increasingly blurred. Recent data indicates a stark disparity in cybersecurity investment levels between high-profile federal agencies and the municipal entities that manage daily essential services. This gap creates a significant vulnerability that state actors are eager to exploit during times of heightened tension.
These local organizations often operate within a target-rich but resource-poor environment, lacking the sophisticated detection tools required to identify state-sponsored persistence. Major market players and credit rating agencies have begun to recognize this systemic weakness, increasingly viewing cyber resilience as a core component of financial stability rather than a secondary technical concern. The influence of these agencies is reshaping how public and private entities prioritize their security budgets, as the threat of a credit downgrade now looms as large as the threat of a data breach.
Emerging Threats and the Expanding Scope of State-Sponsored Aggression
Predatory Tactics and the Evolution of Modern Cyber Warfare
State-sponsored actors like MuddyWater have transitioned from simple disruptive tactics to sophisticated long-term prepositioning within critical networks. These groups often spend months or even years establishing a presence, mapping out operational technology and identifying the most damaging points of failure for future activation. This patient approach allows for a rapid deployment of destructive tools when geopolitical triggers occur. Alongside these professional units, ideological hacktivists and opportunistic cybercriminals exploit the fog of war to launch campaigns that confuse emergency responses and erode public trust.
The focus of these attacks has shifted significantly from traditional information technology systems toward industrial control systems and operational technology. The use of malware, data-wiping tools, and massive denial-of-service operations serves as a potent tool for political signaling, designed to demonstrate the reach of an adversary without engaging in direct physical combat. This technological convergence means that a breach in a digital network can now lead to catastrophic physical failures in the real world, such as the contamination of water supplies or the shutdown of electrical grids.
Projecting the Financial and Operational Impact on Critical Sectors
The financial impact of these incursions is hitting large-scale firms with annual revenues exceeding one billion dollars the hardest, as these entities represent high-value targets for symbolic retaliation. Risk profiles for these organizations have grown exponentially, reflecting their role as the backbone of the national economy. Vulnerable sectors including healthcare, energy, and public finance are seeing a marked increase in performance indicators that signal distress. Consequently, market forecasts show a massive surge in demand for specialized cybersecurity services and resilient hardware as firms rush to fortify their defenses.
Evaluating the potential for systemic disruption in local economies reveals that utility failures are no longer isolated incidents but catalysts for broader economic stagnation. When a municipal power grid is compromised, the resulting downtime affects everything from manufacturing output to the ability of small businesses to process transactions. This ripple effect creates a significant burden on local public finance, as the costs of emergency response and technical remediation drain reserves that were intended for community development and infrastructure maintenance.
Obstacles to Resilience: Vulnerability Profiles and Strategic Challenges
Significant vulnerabilities persist in aging hardware infrastructures, specifically concerning programmable logic controllers like the Unitronics units that were never designed for the modern threat environment. Many decentralized water treatment plants and power distribution nodes rely on legacy systems that lack basic encryption or authentication protocols. This soft underbelly of the national utility system represents a primary target for adversaries seeking to cause widespread public alarm. Protecting these systems is a daunting task that requires a complete overhaul of how industrial processes are managed and secured.
Overcoming specialized staffing shortages remains one of the greatest hurdles for local government and municipal finance departments. There is a fierce competition for talent, and smaller public entities often cannot match the salaries offered by private technology firms. This lack of expertise leads to a reliance on external contractors, which can delay response times during an active breach. Balancing the immediate technical recovery costs with the long-term degradation of essential services is a constant struggle for administrators who must operate under tight fiscal constraints.
The Regulatory and Financial Landscape: Compliance, Insurance, and Credit
The insurance market is currently grappling with the implications of war exclusion clauses, which threaten to leave many organizations without financial recourse after a state-sponsored attack. If an incident is legally attributed to a state actor as part of an ongoing conflict, insurers may deny claims, forcing corporations to cover losses directly from their balance sheets. This possibility introduces a secondary layer of financial instability that complicates the long-term planning of critical infrastructure providers. Legal and regulatory hurdles in attributing these attacks make the process of filing claims a lengthy and uncertain endeavor.
Federal law enforcement and agencies like CISA continue to refine standards for domestic defense, yet the burden of implementation falls heavily on local actors. The conflict has had a direct impact on credit ratings for municipal issuers, as analysts now factor cyber vulnerability into their assessment of an entity’s ability to meet its debt obligations. This shift reflects a broader understanding that a single successful breach can lead to massive unbudgeted expenditures that compromise a city’s financial health. Compliance is no longer just a legal requirement but a prerequisite for accessing capital markets at favorable rates.
The Future of National Defense: Innovation and Global Economic Shifts
Innovation in defense is moving toward a state of permanent readiness, characterized by the integration of artificial intelligence in threat detection to counter AI-driven offensive tools. Future growth areas are likely to center on secure-by-design operational technology and resilient industrial hardware that can function even when broader network connections are compromised. This shift reflects a move away from reactive security toward a proactive stance that assumes a state of constant compromise. Global economic conditions continue to influence military doctrine, reinforcing the idea that digital security is a requirement for maintaining national economic output.
The proactive defense of critical infrastructure is no longer an optional security measure but a fundamental requirement for participating in the global economy. As military doctrines evolve to include digital sovereignty as a core tenet, the domestic sector must adapt to a reality where it is always under some form of surveillance or probe. The influence of global shifts in power is felt in the server rooms of small towns as much as in the halls of federal power. This permanent state of readiness requires a continuous investment in both human capital and technological innovation to stay ahead of rapidly evolving threats.
Summary of Systemic Risks and Strategic Recommendations for U.S. Entities
The assessment of systemic risks revealed a profound asymmetry between military strength and digital vulnerability that demanded immediate strategic intervention. It became clear that the financial burden of retaliatory cyber activity fell disproportionately on taxpayers and shareholders who were unprepared for the costs of modern conflict. Strategic recommendations prioritized increased public-private collaboration and the establishment of federal funding streams dedicated specifically to municipal cybersecurity enhancements. Stakeholders recognized that cyber defense functioned as a fundamental pillar of national resilience, requiring a shift in mindset toward a holistic and proactive security posture.
Leaders established new protocols that moved beyond reactive measures to ensure that essential services survived the inevitable digital backlash. By investing in resilient hardware and fostering a new generation of cybersecurity professionals, the nation sought to close the gap between its physical and digital defenses. The lessons learned from this period of heightened tension highlighted the necessity of integrating cyber resilience into the very fabric of national infrastructure planning. Ultimately, the ability to withstand digital aggression was treated as a vital component of national sovereignty, ensuring that the domestic front remained secure regardless of overseas military developments.