The vulnerability of the American power grid has shifted from a theoretical engineering concern to a tangible national security crisis as affordable unmanned aerial systems redefine the perimeter of critical infrastructure. Historically, the safeguarding of energy assets focused almost exclusively on the fence line, utilizing physical barriers and ground-level surveillance to deter human intruders. However, the rapid proliferation of sophisticated, low-cost drones has effectively rendered traditional vertical security measures obsolete. This review examines the current state of grid countermeasure technology, a specialized field that blends radar physics, electronic warfare, and regulatory navigation to protect the vital organs of modern civilization from aerial disruption. As these systems move from experimental stages into standard utility operations, the industry faces the daunting task of bridging the gap between passive monitoring and active defense in an increasingly crowded and contested airspace.
Evolution of Aerial Grid Defense Systems
The transition from terrestrial security to comprehensive airspace protection represents a fundamental paradigm shift in how utilities perceive risk. For decades, a substation was considered secure if its gates were locked and its cameras were operational. This “bottom-up” security model assumed that any threat would originate from the ground. The emergence of grid countermeasure technology has forced a “top-down” reevaluation, acknowledging that the most significant vulnerabilities now exist in the open air above sensitive equipment. This evolution was not merely a reaction to hobbyist interference but a necessary response to the realization that the electrical backbone was never architected to withstand precise, low-altitude aerial incursions.
This shift has been accelerated by the diminishing cost of entry for potential adversaries. Where a coordinated attack once required physical presence and significant manpower, a single operator can now deploy a fleet of drones from miles away. Consequently, the technological landscape has evolved from simple acoustic sensors that could barely distinguish a drone from a lawnmower to integrated multi-modal platforms. These modern systems combine radio frequency (RF) scanning, electro-optical sensors, and thermal imaging to create a cohesive picture of the local sky. The context is no longer just about seeing a drone; it is about establishing a persistent, three-dimensional dome of awareness that traditional security personnel cannot maintain.
Core Components of Counter-UAS Infrastructure
Airspace Awareness: Radar Integration and Signal Processing
At the heart of any effective countermeasure strategy lies the ability to distinguish between harmless environmental noise and a legitimate threat. Compact, low-altitude radar systems have become the gold standard for this task because they provide active detection regardless of lighting or weather conditions. Unlike traditional aviation radar, which is tuned for large, fast-moving aircraft, these specialized units utilize high-frequency signals to identify small, slow-moving objects with low radar cross-sections. This is a significant technical achievement, as the system must filter out “clutter” such as birds, swaying trees, and precipitation, which can often mimic the flight signatures of small drones.
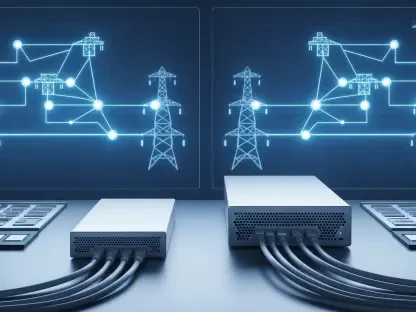
Integration with command-and-control (C2) platforms is what transforms these individual sensors into a functional defense network. These platforms aggregate data from multiple nodes, using machine learning algorithms to analyze flight patterns and telemetry. By identifying the unique RF fingerprint of a drone’s control link, the system can often determine the make and model of the intruder before it is even within visual range. This level of awareness is critical because it allows utility operators to transition from a reactive posture to a predictive one, providing the precious seconds needed to initiate emergency protocols or alert local authorities.
Interdiction and Mitigation Mechanisms: Disruption and Its Limits
Once a threat is identified, the technological focus shifts to neutralization, which is the most complex and controversial aspect of grid defense. Currently, the primary non-kinetic method involves electronic jamming, which floods the drone’s communication frequencies with noise, forcing it to enter a “fail-safe” mode—typically landing or returning to its launch point. However, this implementation is fraught with technical trade-offs. Jamming is an indiscriminate tool; if not precisely targeted, it can disrupt legitimate communications, including emergency radio bands or the utility’s own wireless control systems. This necessitates the use of directional “soft-kill” technologies that focus energy on a specific point in space.
Kinetic interdiction, such as net-launching drones or physical interceptors, offers an alternative but introduces a new set of risks. The physical destruction of a drone over a high-voltage transformer station could lead to the very catastrophic failure the system is designed to prevent. Falling debris or triggered payloads represent a significant hazard to the delicate cooling fins and pressurized insulators found in large power transformers. Therefore, current mitigation research is focused on “capture-and-carry” methods, where an interceptor drone physically entangles the intruder and transports it to a safe zone. This requires immense processing power and agility, as the system must calculate intercept vectors in real-time against an evasive target.
Emerging Trends in Asymmetric Warfare Defense
The threat landscape is currently defined by a massive imbalance in the cost of conflict, a reality that has fundamentally altered the defense industry’s trajectory. A commercial drone costing less than a thousand dollars can be equipped with a simple conductive filament or a small explosive charge capable of disabling a transformer that costs millions of dollars and takes years to manufacture. This asymmetric reality has pushed the industry toward developing “low-cost-per-kill” solutions. Utilities can no longer rely on expensive, military-grade missiles to defend against swarms of inexpensive drones; the economics of such a defense are simply unsustainable.
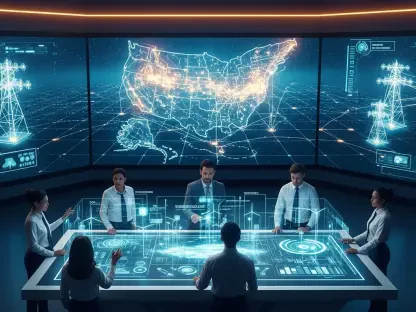
Furthermore, the rise of autonomous drone swarms has introduced a layer of complexity that single-target systems cannot handle. Modern defense trends are moving toward distributed sensor networks that use “hive mind” logic to track multiple threats simultaneously. Geopolitical tensions have also influenced industry behavior, with nation-state adversaries increasingly viewing the power grid as a theater for grey-zone aggression. This has led to a focus on hardened electronics and “spoofing” technologies that can take over a drone’s GPS coordinates, tricking it into flying away from the target without the need for high-powered jamming.
Industrial Applications and Critical Infrastructure Protection
In practical application, these technologies are being deployed most aggressively at nuclear generating stations and major transmission hubs. For a nuclear facility, the stakes are exceptionally high, as a drone-initiated fire or structural breach could have environmental consequences. Here, detection data is not just used for immediate response but is fed into broader risk-management models. By analyzing the frequency and timing of drone incursions, security teams can predict physical or cyber assault patterns. For instance, repeated drone activity at a specific hour may indicate reconnaissance designed to identify security shift changes or maintenance windows.
In switchyards and transformer stations, the application is often about preventing “nuisance” attacks that aim to cause localized blackouts and economic damage. Utilities are increasingly utilizing detection metadata to coordinate with cyber-defense teams. There is a growing understanding that an aerial drone might not be the primary weapon but rather a mobile signal-sniffing platform or a bridge to bypass an “air-gapped” network. By monitoring the RF emissions of drones near sensitive control centers, utilities can detect attempts to intercept wireless traffic or inject malicious commands into the supervisory control and data acquisition (SCADA) systems.
Regulatory and Technical Implementation Challenges
The most significant hurdle to widespread adoption remains the “Regulatory Catch-22.” In the United States, federal law classifies even the smallest hobbyist drone as an “aircraft,” granting it legal protections similar to those of a commercial airliner. This means that while a utility can see a drone approaching its most sensitive equipment, it often lacks the legal authority to touch it, jam it, or bring it down. The Federal Aviation Administration (FAA) maintains strict control over the national airspace, and any unauthorized interference with an aircraft—even one clearly engaged in a hostile act—can result in federal felony charges for the utility operator.
This legal framework has created a gap between what the technology can do and what the law allows. Ongoing development efforts are focused on creating “authorized interdiction zones” around critical infrastructure, but progress is slow. Technical challenges also persist in the form of signal saturation in urban environments. In a city, the air is thick with Wi-Fi, cellular, and radio signals, making it incredibly difficult for sensors to isolate the low-power control links of a rogue drone. This necessitates a level of signal processing sophistication that often exceeds the budgets of smaller municipal utilities, leading to a fragmented security landscape where only the largest entities are truly protected.
Future Trajectory of Grid Security Technology
The path forward for grid security is defined by the integration of state and federal defense frameworks. The National Defense Authorization Act (NDAA) has recently expanded the authorities of domestic agencies to better coordinate with private sector utilities, signaling a shift toward a unified national defense posture. This will likely lead to the creation of standardized “Counter-UAS as a Service” models, where specialized government or private contractors provide the hardware and legal authority to monitor and protect airspace on behalf of utility companies. This approach would centralize the legal liability and technical expertise required to manage active interdiction.
Moreover, breakthroughs in automated drone defense are expected to remove the human-in-the-loop requirement for initial threat response. AI-driven systems are being developed to execute “pattern-of-life” analysis, automatically identifying and flagging any aerial behavior that deviates from the norm. As these systems become more reliable, the focus will shift toward “hardened” infrastructure that can automatically trigger physical countermeasures, such as retractable covers for sensitive equipment or localized electromagnetic pulses (EMP). The integration of these defenses into the very fabric of the grid will be essential for maintaining resilience in an era of persistent aerial surveillance.
Summary of Findings and Industry Outlook
The review of grid countermeasure technology highlighted a critical transition from passive ground security to active, volumetric airspace defense. The industry recognized that the traditional reliance on physical perimeters was insufficient against the agility and low cost of modern unmanned systems. Technological advancements in compact radar and multi-modal sensing provided the necessary awareness, yet the legal framework remained a significant bottleneck for effective interdiction. The analysis showed that while detection capabilities reached a high level of sophistication, the ability to neutralize threats was hampered by federal regulations that protected drones as legitimate aircraft.
The assessment concluded that the future of grid security depended on a collaborative effort between technology developers and policymakers. The transition toward automated, AI-driven defense systems represented the most promising path for scaling protection across thousands of vulnerable substations. Ultimately, the role of counter-UAS technology was established as a vital component of national security, ensuring that the energy infrastructure remained resilient against both nuisance interference and coordinated asymmetric attacks. The evolution of this field proved that securing the backbone of modern society required a constant adaptation to the shifting threats in the sky.