The synchronization of kinetic military operations with aggressive digital disruption has fundamentally transformed the landscape of modern warfare, forcing domestic infrastructure to stand as a primary line of defense. As regional tensions reach a boiling point, the boundary between foreign battlefields and local utility grids has effectively dissolved. This shift represents a transition from isolated hacking incidents to a continuous state of digital siege where the stability of the public sector is directly tied to international diplomacy and military maneuvers.
The Escalation of Digital Retaliation in Global Conflict
Statistical Growth and Market Vulnerability Data
Current data from CyberCube reveals a sobering reality for the American corporate landscape, indicating that 12% of U.S. firms with annual revenues exceeding $1 billion are currently vulnerable to state-linked cyber activities. This vulnerability is not evenly distributed but is concentrated within the energy, healthcare, and utility sectors, which serve as the backbone of national resilience. The trajectory of these hostilities has reached a peak following the recent military campaigns, demonstrating a nearly perfect correlation between physical strikes in the Middle East and a surge in digital probing across the Atlantic.
This surge is characterized by a sophisticated strategy known as prepositioning, where state-sponsored entities like MuddyWater infiltrate networks months or even years before an active conflict begins. Intelligence reports suggest these actors have been quietly establishing persistence within American networks, waiting for a geopolitical trigger to activate disruptive payloads. Moreover, the risk is particularly acute for the public finance sector, where municipal and local entities often operate on legacy systems. These organizations historically underinvest in cybersecurity, making them attractive targets for adversaries looking to cause widespread civilian discomfort with minimal effort.
Real-World Applications and Critical Points of Failure
The practical application of these threats is most evident in the targeting of Unitronics programmable logic controllers, which are widely utilized in water management and industrial control systems. By exploiting these specific devices, attackers can manipulate water pressure or chemical levels, turning essential services into potential hazards. Such incidents highlight the fragility of “soft” targets that lack the robust defense layers found in federal or military networks. During the recent repercussions of the joint U.S.-Israeli campaign, these domestic vulnerabilities were exploited to send a clear message of retaliatory capability.
Furthermore, the regional reach of these cyber actors extends far beyond the primary combatants, affecting surveillance and communication networks throughout the Persian Gulf. These disruptions are designed to blind regional allies and complicate the logistical coordination of Western coalitions. Alongside state-led efforts, a secondary wave of hacktivists and lone wolves has emerged, utilizing distributed denial-of-service attacks to capitalize on general instability. These non-state actors often target healthcare organizations and power providers, creating a chaotic environment that forces domestic agencies to divert resources away from high-level defense.
Industry Perspectives on Financial and Operational Risk
Credit rating agencies such as Fitch and Moody’s have begun to sound the alarm regarding the long-term degradation of creditworthiness following cyber-induced service disruptions. When a utility provider or local government suffers a total system blackout or a massive data breach, the recovery costs can be astronomical, leading to immediate financial instability. Analysts point out that the damage is not merely technical; it is a fundamental destruction of the trust relationship between service providers and their customers. Once data-wiping attacks erase years of records, the path to restoring operational normalcy becomes fraught with legal and reputational hurdles.
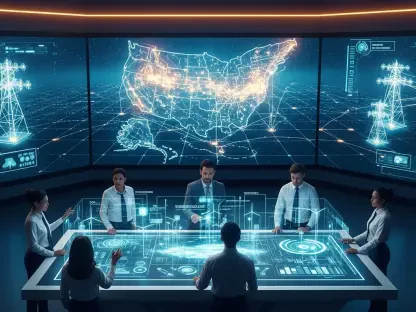
The insurance industry is currently grappling with the “War Exclusion” dilemma, a contentious issue that could leave many organizations without a safety net. If an insurer deems a cyberattack to be a direct act of war or a state-sponsored retaliation, they may deny coverage based on standard policy exclusions. This possibility places an immense burden on corporations and municipalities, which may find themselves forced to cover recovery costs directly from their balance sheets. Federal authorities from CISA and the FBI have emphasized that bridging the gap between foreign military policy and domestic digital defense is no longer optional but a matter of national economic survival.
Future Projections and the Evolution of the Dual-Front War
The intersection of underfunded municipal budgets and sophisticated state-sponsored capabilities is creating what experts describe as a perfect storm. As local governments struggle to balance their books, they remain unable to compete with the resources of a foreign intelligence agency. This disparity suggests that the domestic front will remain a viable target for any nation-state seeking to exert pressure on American foreign policy. Over the coming years, the economic implications of credit downgrades for these entities will likely trigger a restructuring of how public infrastructure is funded and protected.
Strategic evolution in this space is moving toward the development of “blindness” strategies, where cyber actors prioritize disabling surveillance and communications over direct physical destruction. By knocking out the sensors and data links that allow a city to function, an adversary can create a vacuum of information that facilitates broader regional objectives. Additionally, the role of AI and automation is set to expand on both sides of the digital fence. While attackers use AI to identify vulnerabilities at a rapid pace, the defense of critical assets will increasingly rely on automated response systems that can neutralize threats in milliseconds, well before a human operator can intervene.
Summary and Strategic Outlook for Infrastructure Resilience
The critical link between kinetic military actions in the Middle East and the digital vulnerabilities of U.S. infrastructure was unmistakably clear. The events surrounding the recent conflict served as a catalyst for a necessary shift in how the nation views its internal security. It was no longer sufficient to treat cybersecurity as a matter of technical maintenance; it became a core component of comprehensive risk management that accounted for global geopolitical triggers. This realization forced a move toward more integrated defense strategies that prioritized the continuity of essential services during times of international crisis.
The necessity of federal support for municipal cybersecurity became a primary focus to preserve the stability of the public finance market. By providing the resources needed for local governments to harden their networks, the federal government took steps to ensure that the domestic front did not become the weakest link in the national defense chain. Moving forward, the resilience of infrastructure was defined not just by the strength of its walls, but by the agility of its digital defenses and the robustness of its financial safeguards. These actions laid the groundwork for a more secure and stable future in an increasingly interconnected and volatile global landscape.