The vulnerability of the modern electrical grid is often hidden behind technical jargon and regulatory classifications that fail to account for the sophisticated nature of contemporary digital threats. While the North American Electric Reliability Corp. (NERC) utilizes a Critical Infrastructure Protection (CIP) framework to categorize power generation facilities, the distinction between high and low impact labels is fundamentally a measure of load reliability rather than a reflection of cybersecurity resilience. A small-scale solar farm or a rural wind project might be labeled as low impact because its individual removal from the grid does not trigger an immediate blackout, yet this designation frequently creates a dangerous sense of complacency among operators and stakeholders alike. In a landscape where digital connectivity is ubiquitous, the assumption that a facility is too small to matter provides a perfect veil for adversaries looking to exploit the weakest links in the national energy infrastructure without drawing immediate attention.
This disparity between regulatory status and actual risk has become a focal point for security experts who argue that the current classification system is increasingly detached from the realities of the field. When a facility is designated as low impact, it is often exempt from the most stringent cybersecurity controls, such as rigorous multi-factor authentication, advanced intrusion detection systems, and frequent third-party auditing. Consequently, these sites become soft targets that serve as entry points into larger, more sensitive networks. The threat is not merely the loss of a few megawatts of power but the potential for an attacker to use a compromised low impact site as a persistent staging ground for lateral movement across the utility’s broader corporate and operational environments. As the industry moves further into a period of rapid digital transformation, closing this security gap is no longer optional but a necessity for national stability.
The Danger of Distributed Vulnerabilities
Understanding Cumulative Grid Impact
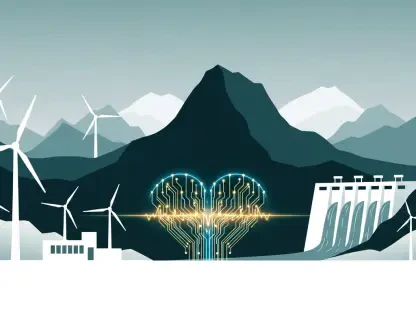
The shift toward a decentralized energy landscape has fundamentally altered the mathematical reality of grid stability, moving away from a model dominated by a few massive coal or nuclear plants toward an intricate web of distributed energy resources. In 2026, the proliferation of wind, solar, and battery storage systems means that the collective output of these low impact sites now constitutes a significant portion of the total energy mix. While the loss of a single ten-megawatt facility remains statistically insignificant, the simultaneous removal of dozens or hundreds of such facilities can overwhelm the grid’s ability to balance supply and demand. Because these distributed sites often rely on identical hardware and software configurations provided by a handful of major vendors, they possess a shared vulnerability profile that an attacker can exploit at scale to achieve a massive, coordinated disruption.
A sophisticated cyberattack targeting these synchronized vulnerabilities can bypass traditional reliability safeguards by triggering what is known as a cascading failure or a domino effect. When multiple small sites are taken offline simultaneously, the sudden drop in generation causes frequency and voltage levels to fluctuate wildly beyond their designated safety parameters. In response, automatic protection relays—designed to prevent physical damage to transformers and other expensive hardware—will trip, disconnecting even healthy parts of the grid to save the equipment. This reactive behavior, while necessary for hardware preservation, accelerates the blackout, turning a series of minor, low impact events into a regional or national crisis. This collective risk highlights why the security of a single small site cannot be viewed in isolation from its role within the wider interconnected ecosystem of the power network.
Managing the Risks of Interconnectivity
Beyond the immediate loss of generation, the high level of interconnectivity between low impact sites and central control centers introduces a secondary layer of risk that is often underestimated. Modern grid operations require constant communication between field devices and supervisory control and data acquisition systems to manage real-time balancing and market functions. These communication channels, if not properly secured, provide a pathway for malicious actors to inject false data or issue unauthorized commands that could confuse grid operators or damage physical assets. The reliance on standardized protocols like DNP3 or Modbus, which were frequently designed without robust encryption or authentication features, means that an intruder who gains access to a remote solar site could potentially spoof telemetry data for an entire region.
Furthermore, the integration of third-party managed services for maintenance and monitoring adds a complex layer of supply chain risk to the low impact facility equation. Many smaller operators outsource their digital management to specialized firms that handle dozens of different sites across various utility territories. If one of these service providers is compromised, the attacker gains a “keys to the kingdom” scenario, allowing them to access a vast array of supposedly low impact facilities simultaneously. This centralized point of failure contradicts the decentralized nature of the physical assets, creating a bottleneck where security is only as strong as the most poorly protected service account. Protecting the grid now requires a move away from siloed security thinking toward a holistic model that accounts for the fluid movement of data and access across multiple administrative boundaries.
The Limitations of Current Standards
Moving Beyond the Compliance Trap
One of the most pervasive issues facing the energy sector is the compliance trap, a phenomenon where utility operators confuse meeting the minimum legal requirements of NERC CIP with achieving an actual state of security. Regulatory standards are, by their very nature, reactive and slow to adapt; the process for drafting, vetting, and implementing a new NERC requirement can take several years, during which time the threat landscape has already shifted. For a low impact facility, the requirements are notably light, often focusing on basic physical security and rudimentary electronic access controls. This creates a situation where a plant can be one hundred percent compliant with the law while remaining completely vulnerable to a modern ransomware strain or a state-sponsored advanced persistent threat that targets unpatched software vulnerabilities.
This reliance on a compliance-first mindset often leads to a “set it and forget it” approach to security, where upgrades are only performed when mandated by a change in the rules. In contrast, effective cybersecurity in 2026 requires a continuous, threat-informed strategy that evolves as quickly as the adversaries do. When operators treat regulations as the ceiling rather than the floor, they fail to invest in the proactive monitoring and hunting capabilities necessary to detect an intruder before they can cause damage. The goal must shift from simply avoiding a regulatory fine to building a resilient operational environment that can withstand and recover from an inevitable breach. True security is an ongoing process of assessment and refinement, not a static checkbox on a government form that is only revisited during an audit cycle.
Evaluating Regulatory Lag and Technological Shifts
The disconnect between the speed of technological innovation and the pace of regulatory updates is particularly evident in the deployment of edge computing and artificial intelligence at low impact sites. Many newer facilities utilize AI-driven optimization tools to manage battery discharge cycles or predict solar output, yet the cybersecurity implications of these technologies are rarely addressed in current standards. These advanced systems introduce new attack surfaces, such as model poisoning or data manipulation, which traditional NERC CIP frameworks were never intended to mitigate. As the grid becomes smarter and more autonomous, the lag in regulatory coverage leaves these sophisticated components in a legal and security gray area where their protection is left entirely to the discretion of the owner.
Moreover, the global nature of the energy hardware supply chain complicates the task of maintaining compliance while ensuring actual security. A utility might purchase a set of inverters or controllers that meet all current North American standards, only to discover later that the firmware contains “backdoor” vulnerabilities or undocumented features that could be exploited. Since low impact facilities are not typically required to perform the same level of deep-dive supply chain analysis as high impact sites, these vulnerabilities often go undetected for years. Bridging this gap requires a fundamental change in how the industry views the lifecycle of an asset, moving toward a model where security is verified at every stage—from manufacturing and shipping to installation and eventual decommissioning—regardless of the site’s official reliability rating.
Technical and Operational Gaps
Identifying Structural Weaknesses
Field assessments of low impact power plants frequently reveal a “Frankenstein” architecture, where cutting-edge digital control systems are integrated with legacy mechanical components that have been in service for decades. This hybridization creates significant security blind spots because older equipment was often designed for an era when “air-gapping” was the primary defense and network connectivity was non-existent. When these legacy devices are connected to modern gateways to facilitate data collection, they often lack the processing power to support encryption or modern logging functions. This leaves them exposed and unable to defend themselves against even basic network-based attacks, providing an easy foothold for an adversary to gain control over physical processes like breaker operations or turbine speeds.
In addition to hardware limitations, many low impact facilities suffer from a lack of accurate operational documentation, which severely hampers incident response efforts. It is not uncommon to find that network diagrams are years out of date or that hardware inventories do not reflect the actual devices currently connected to the network. This lack of visibility means that if a security event occurs, the response team may not even know which devices are under attack or how they are connected to the rest of the system. Without a clear and real-time understanding of the digital footprint of a facility, it is impossible to implement effective monitoring or to identify “shadow IT” devices that may have been added by contractors or maintenance teams without official authorization or security vetting.
Addressing Unauthorized Access and Configuration Drift
The rise of remote work and the need for operational efficiency have led to a surge in remote access points at low impact sites, many of which are poorly managed or entirely undocumented. Maintenance teams and third-party vendors often require remote connections to troubleshoot equipment or perform software updates, but these pathways are frequently left open long after the work is completed. If these connections do not utilize strong, centralized identity and access management, they become a primary vector for credential stuffing attacks or brute-force entries. An attacker who gains a single set of valid credentials can often move through the entire operational network because internal segmentation is frequently non-existent in low impact environments, allowing them to jump from a non-critical sensor to a primary controller.
Configuration drift also presents a major operational risk, as small, unauthorized changes to system settings accumulate over time and weaken the overall security posture. In the fast-paced environment of power generation, personnel might temporarily disable a firewall rule or change a password to “admin” to simplify a troubleshooting task, only to forget to revert the change once the issue is resolved. These incremental lapses create a “Swiss cheese” effect where multiple small vulnerabilities eventually align to create a major opening for an intruder. Managing this risk requires the implementation of automated configuration monitoring tools that can detect and alert on any unauthorized changes in real-time. By ensuring that systems remain in a known, hardened state, operators can significantly reduce the likelihood that a minor human error will escalate into a major security breach.
Building a Proactive Defense
Implementing Security-by-Design
To move beyond the limitations of the current classification system, the power industry must adopt a “security-by-design” philosophy that treats every generation asset as a potential high-impact target. This approach involves integrating security considerations into the very beginning of the project lifecycle, during the engineering and procurement phases, rather than trying to “bolt on” protections after a plant is already operational. By selecting hardware with built-in security features—such as secure boot, hardware-based encryption, and signed firmware—utilities can ensure that their foundational infrastructure is resilient against tampering. This proactive stance significantly reduces the long-term costs of security by eliminating the need for expensive retrofits and reducing the overall complexity of the defensive architecture.
A critical component of this design philosophy is the implementation of rigorous network segmentation, which acts as a digital containment system to prevent the spread of a cyber-infection. By dividing the facility’s network into smaller, isolated zones based on function and risk, operators can ensure that a compromise in a low-priority area, like a weather station or a business office, cannot reach the critical programmable logic controllers that manage the flow of electricity. This “zero trust” approach assumes that a breach is always possible and focuses on limiting the attacker’s ability to do damage once they are inside. Combined with continuous, real-time traffic monitoring, segmentation allows for the rapid isolation of affected systems, ensuring that the facility can continue to operate in a degraded state even while under active attack.
Enhancing Visibility and Incident Readiness
Maintaining a high level of operational resilience also requires a commitment to comprehensive asset visibility and sophisticated logging practices that go far beyond regulatory requirements. In 2026, the use of passive network monitoring tools has become an industry standard for those who wish to truly secure their assets; these tools can identify every device on the network and alert operators to any unusual behavior without interfering with sensitive industrial processes. By establishing a clear baseline of “normal” network activity, security teams can quickly spot the subtle anomalies—such as a controller communicating with an unknown external IP address—that often signal the early stages of a sophisticated cyber-operation. This early detection is the key to stopping an attack before it reaches the stage where it can impact grid reliability.
Finally, the transition to a more secure future requires a cultural shift within utility organizations to prioritize incident readiness and cross-functional collaboration. Cybersecurity is no longer just an IT problem; it is a fundamental operational risk that requires the active participation of plant engineers, operations staff, and executive leadership. Regular “tabletop” exercises and simulated cyber-physical attacks should be conducted to ensure that all personnel know exactly how to respond when a breach is detected, including how to transition to manual operations if digital systems are compromised. By fostering a culture of constant vigilance and continuous improvement, the industry can ensure that the “low impact” label never again serves as a bypass for the security of the North American power grid. The path forward involves turning these overlooked sites into hardened bastions of the energy transition, proving that in a truly resilient system, no asset is too small to be defended with the highest level of professional rigor.
The industry moved toward a more integrated defense model that prioritized the safety of the entire grid over the individual classification of its components. Leaders recognized that the previous reliance on static compliance had failed to account for the speed of digital evolution and the creativity of modern adversaries. By implementing these actionable strategies—starting with absolute asset visibility and moving toward automated, real-time threat detection—utilities successfully transformed their most vulnerable sites into resilient nodes of a modernized network. The focus shifted from merely surviving audits to actively hunting for vulnerabilities and hardening systems against the unknown, ensuring that the lights stayed on across the continent regardless of the challenges posed by an increasingly connected world.